Security Centre
Security is the most important thing to manage in the crypto space. We want to ensure you are safe, protect your crypto-assets and understand some of the security pitfalls.
The Security Centre is your go-to area for quick tips to protect yourself right away, keep up to date with the security information, resources to level up your security and links to our community if you’re confused or spot a potential scam.
Importance of Crypto Security
Owning and storing your crypto-assets means you’re essentially your own bank and are responsible for safeguarding them. That’s why it’s essential to take the correct steps to maximise your security, understand common pitfalls and minimise your exposure to the risk of loss or theft.
The Security Centre is your hub for learning about crypto security:
- Best practices
- Where to find help
- Things you can do right now to protect yourself
- Security and scam resources
- Security updates
6 Ways To Protect Yourself Right Now
Many security vulnerabilities can be mitigated by following the 6 essential rules below.
#1: The Golden Rule: Never share your recovery phrase and be wary of imposters
Your recovery phrase is the 12 or 24 words that act as your backup if you lose your account or device. You should never share your seed phrase with anyone. This is only for your eyes. Sharing it is the easiest way to lose your crypto.
If you’ve been approached by someone else to back up or reset your wallet, this should be a red flag—Collective Shift, Ledger or any crypto-organisation will never privately message you asking for your passwords, private keys or recovery phrase.
When contacting Collective Shift, please verify that you received communication from our official accounts—see our official links at Verify Collective Shift.
Tip: The only time you should enter your recovery phrase is to restore a wallet—making sure you are on the official website and doing so on your own accord.
#2: Activate 2-Factor Authentication (2FA) across all accounts
Use an authenticator app such as Authy or Google Authenticator. If a hacker can guess or obtain your login information (which is easier than you may expect), they’ll require an extra login just in case. Activating 2FA across all exchange accounts and your social media or personal accounts is highly recommended.
Tip: Avoid using SMS for your 2FA
Read: What Is Two-Factor Authentication (2FA)?
Collective Shift members can now activate 2FA—Head to Security Settings or view our walkthrough!
#3: Use hardware or cold wallet to separate your main crypto stack from the internet
A hardware wallet requires you to manually plug in and type on a device to move your cryptocurrency. At the very least, a cold wallet—a fresh wallet not connected to the internet—will ensure your crypto cannot be accessed in the event your computer is compromised.
- Cold wallet = Not connected to the internet.
- Hot wallet = Connected to the internet
It’s best practice to separate long-term crypto-asset holdings from your daily crypto wallet, including prized or higher value NFTs. In the unfortunate event you’re attacked by a phisher, your main stack will be safe. Only connect your wallet to trusted websites.
Tip: A hardware wallet is often needed when your crypto-assets are worth thousands of dollars.
Read: Ultimate Guide to Storing Your Cryptocurrency
#4: Store your wallet information safely—ideally offline
Whenever writing down your seed or recovery phrases, ensure you do so by hand (i.e. offline). Saving your crypto passwords, private keys or recovery phrases in a text document on your computer is an easy attack vector.
Tip: To take another step in security you may want to look into advanced seucity options such as storing backs up in safety deposit boxes or multi-sig (advanced) for expectionally large sums.
Read: Ultimate Guide to Storing Your Cryptocurrency
#5: Be on phishing alert
Phishing is when you get tricked into thinking you’re on an official website that is not legitimate. Scammers will try to make you think you’re on an official website—when it’s just a fake website disguised to match the look and feel of the legitimate site. If you sign your wallet to the website, then you could have your wallet funds drained.
It’s important to check the URL when accessing sites via Google or getting emails from supposed crypto organisations. Be ultra cautious when using new websites, not from official links.
Tip: Bookmark your commonly used crypto exchanges, communities or games, and get in the habit of clicking those bookmarks.
Read: What Is Phishing? (with example)
#6 When setting up a new wallet, test it first!
Although many people do the right thing and set up a cold or hardware wallet when they restore the recovery phrase or wallet, it no longer works. This may be due to a single error like writing down one word in the wrong spot or mixing up different wallet information.
Test out your wallet back-up after creating it. Try restoring your wallet with the newly created recovery phrase. This saves a LOT of heartbreak later.
Tip: When sending crypto-assets to new wallets always send a small test transaction first! And remember, never send crypto-assets to a contract address.
Advanced Tips
Relatively experienced Web3 and crypto users can also protect themselves by understanding how token approvals can be malicious.
Essentially, whenever you interact with web wallets like MetaMask or Phantom and trade on Uniswap, it’ll ask you to sign your wallet and allow the transaction—this allows approval for the smart contract inside the dApp to swap that particular cryptocurrency. Some malicious phishing websites or illegitimate dapps will try to trick you into signing over control of ALL your cryptocurrencies. Ensure to carefully read the MetaMask pop-up and be wary of any “approval all” requests.
Tip: Once you have allowed a dapp to approve swapping your tokens, this remains active even after you have traded. You can revoke your token approvals, see which dapps still have access, and revoke the ones you no longer trust via Etherscan or Zapper.
See Matt’s 10-minute explainer on token approvals and how to take steps to avoid this issue.
Caution: If you ask for help with security from anyone, remember that no one should ever need to ask you for your logins, passwords, seed phrase or to screen-share.
Other Resources
We have a host of resources to help guide you through security, storage and spotting scams.
- Scam Protection Guide: What You Need To Know To Avoid Crypto & NFT Scams
- Guide to the Latest Wave of Crypto Scams
- Ultimate Guide to Storing Your Cryptocurrency
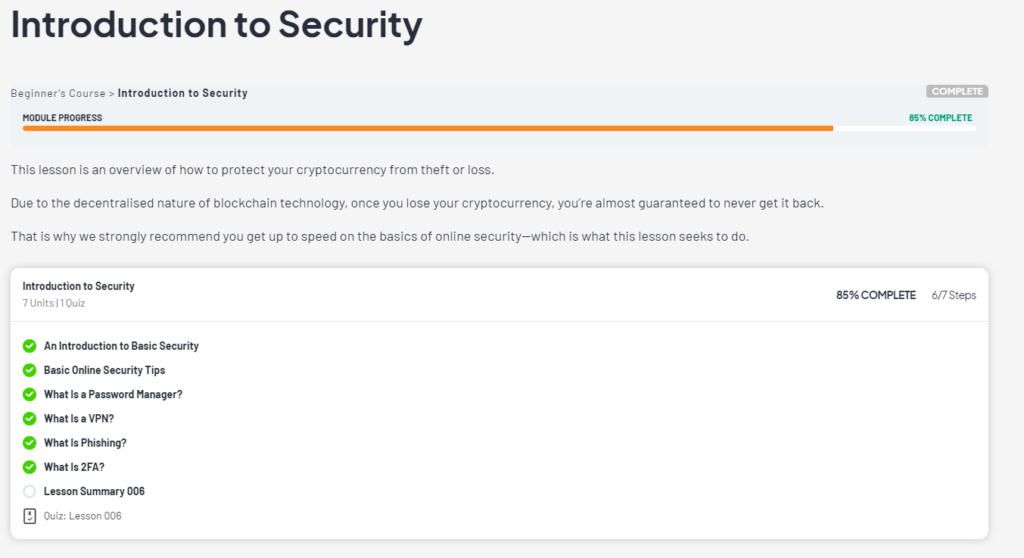
- Introduction to Security — Collective Shift Beginner Course
Third-party resources we highly recommend: